Greetings and welcome, friend.
Hey there! I'm Chris Knepper. I make pixel-perfect apps and websites powered by beautiful code. If you're here, perhaps you were linked here from a page I've done and hopefully you're interested in an app/web developer/designer. If you haven't seen my work, check out my portfolio. I am 27 years old and currently work as a Software Engineer at ThriveHive. I graduated from Rochester Institute of Technology in 2015. For more about me and my history with crafting websites, visit the about page.
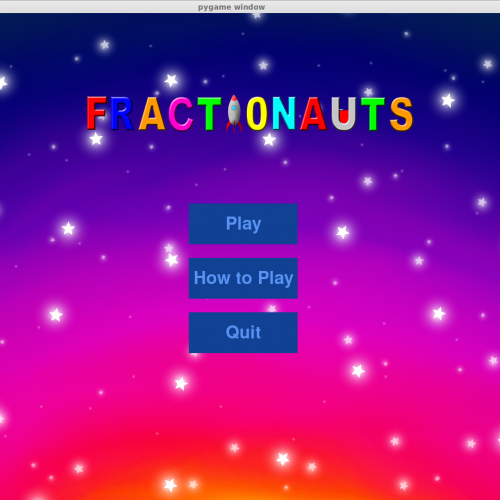
View My Resume (HTML) There's a PDF, too.Stuff I've Done:
- Stuff I Can Do
- HTML5/CSS3
- React Native/React/Angular
- JavaScript/jQuery
- PHP
- MySQL
- Git
- Wordpress
- Adobe Photoshop/Illustrator
- and more…
Stuff I've Said:
Does 0.1 Mean "Usable" or "Useful"? Getting Back into Android More Than Three Final Answers Tasting the Finish Line Three Final Questions US Navy Onions (Profile)Contact
If you want to get in touch with me, fill out this form. I will get back to you as soon as possible!
Thanks for your message! We will get back to you ASAP!